Starting a new business and thinking over to come on internet welcomes you to all new world of E-commerce. The big boom of business start-ups as well as from well-established business firms always sets a window e-commerce. E-commerce is basically exchanging and trading goods, more or less with services from corporations. Another way it is bringing business sections to the ground of internet.
Such an important thing for all the e-commerce websites is there perfect security. After all, it is web, open to world, not a room with a lock. So its protection is really important. Threats can hit in any form; it can come from any window over internet and cause big harm to the authenticity and important data laying in the databases of these websites.
Common threats:
- The base for the website is ultimately their servers and the computer which are their Client through this service. Mainly the threats which are running against the security of online media is Trojan horse, Active contents, Viruses. Along the sides on servers common threats are Privilege setting, Server Side Include (SSI), Common Gateway Interface (CGI), and File transfer, spamming.

- The prone area where the effect of attack is visible is shopping software cart. The routines which are applicable here are online purchasing updates, tracking customer’s details and accounts and bunch of other services. It is all tied up in software. It is basically an operating system. The next point where there is need for security is online payment transaction. The whole system works around with accepting credit cards details through a gateway which is purely online.

- Other such threats are cracking; spoofing, eavesdropping, root kits. The trends also show us threats like System unavailability and denial of service, power interruptions.
Common vulnerabilities:
- SQL Injection: SQL injection is a phenomenon with which malware author insert SQL characters in field of user input. Through this it make such that queries are executed at the back-end of database. IF say the e-commerce website is vulnerable to such attacks, they have the power to attack even the restricted areas of website. Depending upon the knowledge of the attacker, they may steal sensitive data viz. credit card numbers, transaction details, etc. The tendencies of getting such an attack via log in page are common.
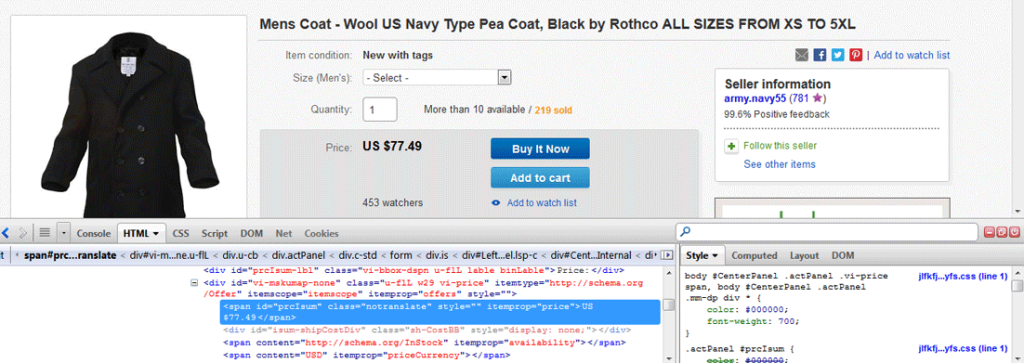
- Price Manipulation: This is vulnerability where the total payable price of the goods purchased is stored over a hidden HTML field, which is dynamically generated by web page. With use of some tools, the modification of payable amount is changed.
- Cross-site scripting: It is because of lack of proper input/output validation by the web application that such circumstances are faced by the websites driving commerce. The forms which are present on such website which are basically for feedback or suggestion about the products, here the malware author can induce his own content and make a whole new script running on the victim’s system. This way they steal sensitive information and session ID’s. It leads to stealing credential of users again.
- Weak Authentication and Authorization: The Authentication mechanisms are simple criteria to breach into the target system by malware authors. Some of system which does not limit the failed log ins often gets to face the circumstances of stealing away the credentials of users or even sometimes leading to fake online purchase being some other person. This way there is huge risk to authentic user’s credentials.

Conclusion:
It is very important to start the base of e-commerce business with the prior knowledge of such security check points. The use of operating systems, language used for bringing up the software and such things help in making the software but at the same point such things drive the path of security breaching as well. Proper security measures should be taken. Confidentiality of the data is important for both who is doing the business and who is participating in the business.

Leave a Reply